
Ransomware continues to sting numerous organizations, and the problem only seems to be getting worse. So, defenders across every type of targeted organization – including government agencies and private businesses – would do well to have more effective defenses in place.
Such defenses would ideally include organizations proactively looking for known ransomware attackers’ tactics, techniques and procedures. That kind of threat hunting can help defenders spot attacks in the reconnaissance phase before they progress to data being exfiltrated or systems getting crypto-locked.
But where to begin?
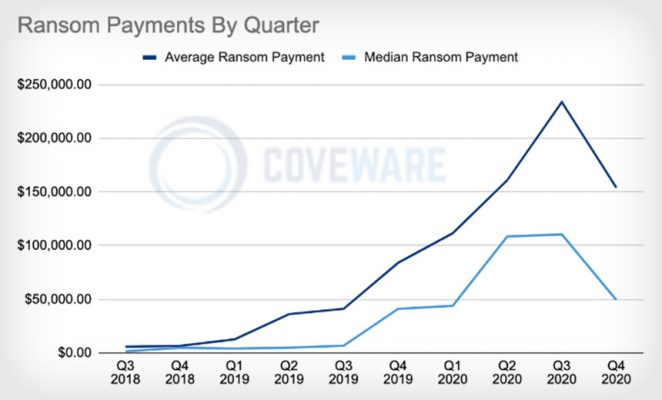
First, perhaps, by acknowledging that the status quo isn’t working. Indeed, ransomware continues to generate large profits for criminals, reports ransomware incident response firm Coveware.
The state of ransomware defenses doesn’t appear to be improving – or at least not as quickly as attackers continue to innovate. Last year, “at least 113 federal, state, county and municipal governments and agencies were impacted by ransomware which, coincidentally, is the exact same number which were impacted in 2019,” security firm Emsisoft reports in a roundup of ransomware trends.
Last year, “globally, more than 1,300 companies, many U.S.-based, lost data including intellectual property and other sensitive information,” Emsisoft says.
That figure only counts organizations that either publicly reported they’d suffered a ransomware infection or had stolen data appear on leaks sites. Because underreporting of crime is widespread, the actual level of ransomware hits is likely far higher than what’s been reported.
But it’s notable that when comparing all of 2019 with 2020, Emsisoft didn’t see growth in the number of ransomware victims.
“The numbers remained relatively flat despite COVID-19 and the transition to remote work,” says Brett Callow, a threat adviser at Emsisoft. “That’s likely because the pandemic caused as many problems for cybercriminal as it did for organizations. Attack surfaces altered, and it took time for threat actors to adjust – which is why the number of incidents dipped significantly in the early days of the pandemic.”
Big Operators Recruit Specialists
Given the potential profits to be made via ransomware, more operations have been joining the fray as well as upscaling, says John Fokker, head of cyber investigations and red teaming for McAfee Advanced Threat Research. He says some of the top skills being sought by successful operations include penetration testing – using tools such as Metasploit and Cobalt Strike. Familiarity with system administration tools and environments, including network-attached storage and backups – for example, using Microsoft Hyper-V – are also in demand, he says.
Gaining access to organizations and retaining that access continue to be a priority, no matter the impact to hacked systems, says Tom Kellermann, head of cybersecurity strategy at VMware.
“In general, ransomware has over 14 different evasion techniques,” he says. Those include virtualization, sandbox evasion, modifying registries, obfuscating files and disabling security tools.
“But most importantly, we need to appreciate that that we’ve seen a renaissance of tootkits. They want to come back. They’re staying in; the persistence is a priority,” he says. “What’s most important now is it changes the game, especially when we’ve seen a surge of counter-incident response, which is occurring 82% of the time now – everything from deleting logs to actually destroying infrastructure or data.”
Attackers’ first priority after breaking in, however, is typically to complicate a victim’s chance of recovering. “They penetrate the backups first to prevent resurrection,” Kellermann says.
Essential Defenses
The mandate is clear for organizations: Have robust ransomware defenses in place, or else.
“Organizations need to be prepared for a ransomware attack,” cybersecurity firm FireEye says in a recent report. “This means ensuring that networks are segmented, that an actual plan is in place and that tabletop exercises have been conducted with senior leaders and other key staff so everyone is ready to take an optimal action. Organizations should have an incident response service-level agreement – SLA – in place. They should also establish secured backups that teams can revert to when necessary.”
Another essential defense: keeping all software up to date. For attacks investigated by incident responders at security firm Group-IB last year, exploiting known flaws that hadn’t been patched “was one of the most popular initial access vectors among threat actors,” and especially for big game hunters, says Oleg Skulkin, the firm’s lead digital forensics specialist. Big game hunting refers to taking down larger targets in the quest for bigger ransom payoffs.
Experts also recommend using multifactor authentication to secure remote desktop protocol and VPN access. Without MFA, attackers only need to brute-force or steal valid credentials to remotely access systems.
“If you have multifactor authentication, even if attackers have proper credentials, it will be impossible for them” to remotely access systems simply by using those credentials, Skulkin notes. Finally, training employees and especially cybersecurity teams to better “prevent and respond to such attacks” remains essential, he notes.
Threat Hunting: 13 TTPs to Beware
To better identify when they’ve been breached, experts recommend organizations seek out ransomware attackers who might be inside their networks. Here are just some of the tactics, techniques and procedures being widely used by ransomware operators in their efforts that organizations should monitor:
- AdFind: This command-line Active Directory tool gets employed – like so many legitimate utilities – by numerous criminals, Group-IB says.
- Advanced IP Scanner: Developer Famatech says its free network scanner “shows all network devices, gives you access to shared folders, provides remote control of computers (via RDP and Radmin), and can even remotely switch computers off.” Group-IB says attackers sometimes drop the tool themselves, or simply download it onto systems from the official website, as part of their network penetration efforts.
- “Banking” Trojans: Trickbot and Qakbot are among the types of malware that began as banking Trojans, but which have been redesigned to help gangs gain initial access to a system and then “drop” other types of malware, including ransomware. Because of the increasing crossover between this type of malware and ransomware, “we think companies should investigate infections more carefully, rather than just reimaging the machine and moving on,” says Ariel Jungheit of Kaspersky Lab’s Global Research and Analysis Team.
- BitLocker Drive Encryption: Unless it’s properly administered, this tool, built into recent versions of Windows, can be used by attackers to forcibly encrypt every PC. “It doesn’t always take a piece of malware to ransom systems,” says Rick McElroy, head of security strategy at VMware.
- ClearLock: This screen-locking tool is used by attackers “so system administrators and other personnel cannot log in and cancel encryption processes,” Group-IB’s Skulkin says.
- Cloud Storage: “Ransomware operators commonly use cloud storage to exfiltrate sensitive data from compromised networks,” Group-IB says. Security firm Sophos says the top three sites attackers use to send exfiltrated data are Google Drive, Amazon Simple Storage Service and the Mega file-sharing service.
- Cobalt Strike: This penetration-testing tool is used by “around 70% of all groups involved in big game hunting,” Skulkin says.
- Exploits: Ransomware gangs target vulnerabilities in remote access services, such as the CVE-2019-11510 flaw in Pulse Secure and flaws in Pulse Secure, Fortinet and Palo Alto products, Skulkin says. Such flaws can give attackers easy, remote access to a victim’s infrastructure. Conversely, experts say keeping such systems patched can drive attackers to look elsewhere.
- IObit Uninstaller: This Windows utility is designed to install unwanted files. Criminals often use the tool to deactivate or help avoid antivirus software.
- Mimikatz: This freely available tool can be used to dump Windows passwords and help attackers escalate privileges. Skulkin says it remains widely used and very often gets deployed without attackers even bothering to rename or attempt to hide it.
- NLBrute: This is designed to brute-force guess a wide range of RDP passwords.
- NS2: Malware-wielding hackers use this utility for mounting available network drives and shares to enable their malicious code to spread farther.
- PsExec: Microsoft calls this “a lightweight telnet-replacement that lets you execute processes on other systems.” Security experts say numerous gangs rely on it to help take down victims.
Preparation Pays
Devoting resources to threat hunting and watching for known TTPs, as well as putting essential defenses in place, won’t stop all ransomware-wielding attackers in their tracks.
“Organizations are going to be targeted and they are going to be compromised, so it is crucial to have prevention and recovery strategies in place,” FireEye says. That includes implementing well-honed incident response strategies.
But anything that an organization can do to make life more difficult for ransomware-wielding attackers may drive criminals to look elsewhere. Likewise, honing response strategies can better blunt the impact of an attack in progress, eject attackers from networks and more quickly mitigate the damage. As with all aspects of ransomware defense, planning pays.
Source: www.inforisktoday.com

 Ελληνικά
Ελληνικά